From Consortium input to new controls: AIUC-1 quarterly update process
AIUC-1's quarterly cadence is deliberately faster than traditional standard-setting processes, enabled by a structured, repeatable process grounded in contributions from AIUC-1 consortium members, technical peer-review, and transparent change management. This quarter, over 120 Consortium members contributed through a series of technical sessions and 200+ peer-review comments.
Standards are only as credible as the process behind them. Broad stakeholder representation, transparency, and detailed peer-reviews are foundational to any standard that earns lasting trust.
AIUC-1's quarterly cadence is deliberately faster than traditional standard-setting processes. This decision is based on clear feedback from enterprise security leaders that the pace of AI capabilities and risks demand a standard that can keep up.
That speed comes with a responsibility: a more transparent process, tighter feedback loops, and an iterative approach where, for example, emerging best practices are integrated as optional requirements initially and areas where consensus is absent are investigated further through dedicated working groups.
Every quarterly cycle follows a structured, repeatable process grounded in contributions from AIUC-1 consortium members, technical peer-review, and transparent change management. Below, we highlight each step in more detail.
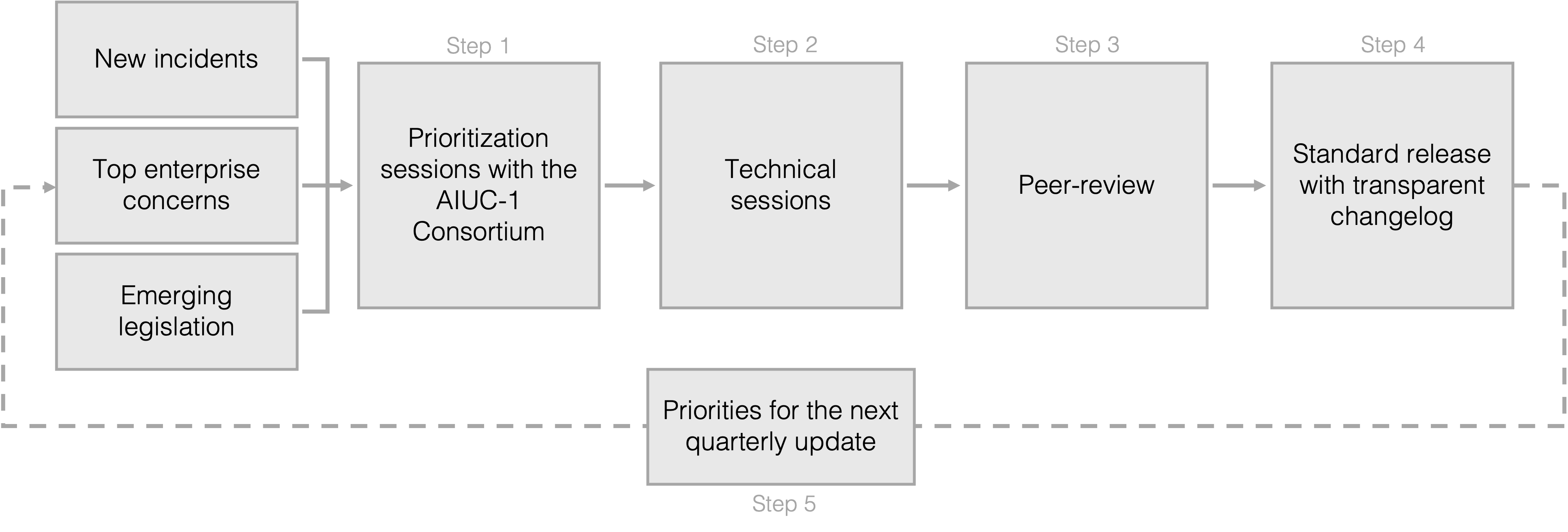
The AIUC-1 quarterly update process
An executive summary of the standard updates this quarter can be found here.
Step 1: Identifying priority areas
AIUC-1 is shaped quarter by quarter through the AIUC-1 Consortium, which unites CISOs, GRC leaders, practitioners, and academics from leading organizations around the world. Members include security executives, experts and practitioners from Salesforce, JP Morgan, HubSpot, Cisco, Meta, MongoDB, Databricks, Cloudflare, Stanford, MIT, OWASP, MITRE, CSA, and more than 200 other organizations.
The AIUC-1 Consortium acts as a working group, ensuring that AIUC-1 is a truly industry-led standard. Members guide standard priority areas, contribute line-level feedback on requirements, debate controls in live sessions, and bring real-world enterprise risk experience - all of which feeds directly into the standard.
Alongside Consortium input, each quarterly update is guided by real-world AI incidents and emerging AI legislation.
This quarter, members surfaced the risks and gaps most pressing in their organizations, and determined this quarter's priority areas: MCP and A2A protocol security, and agent identity, permissions and access management.
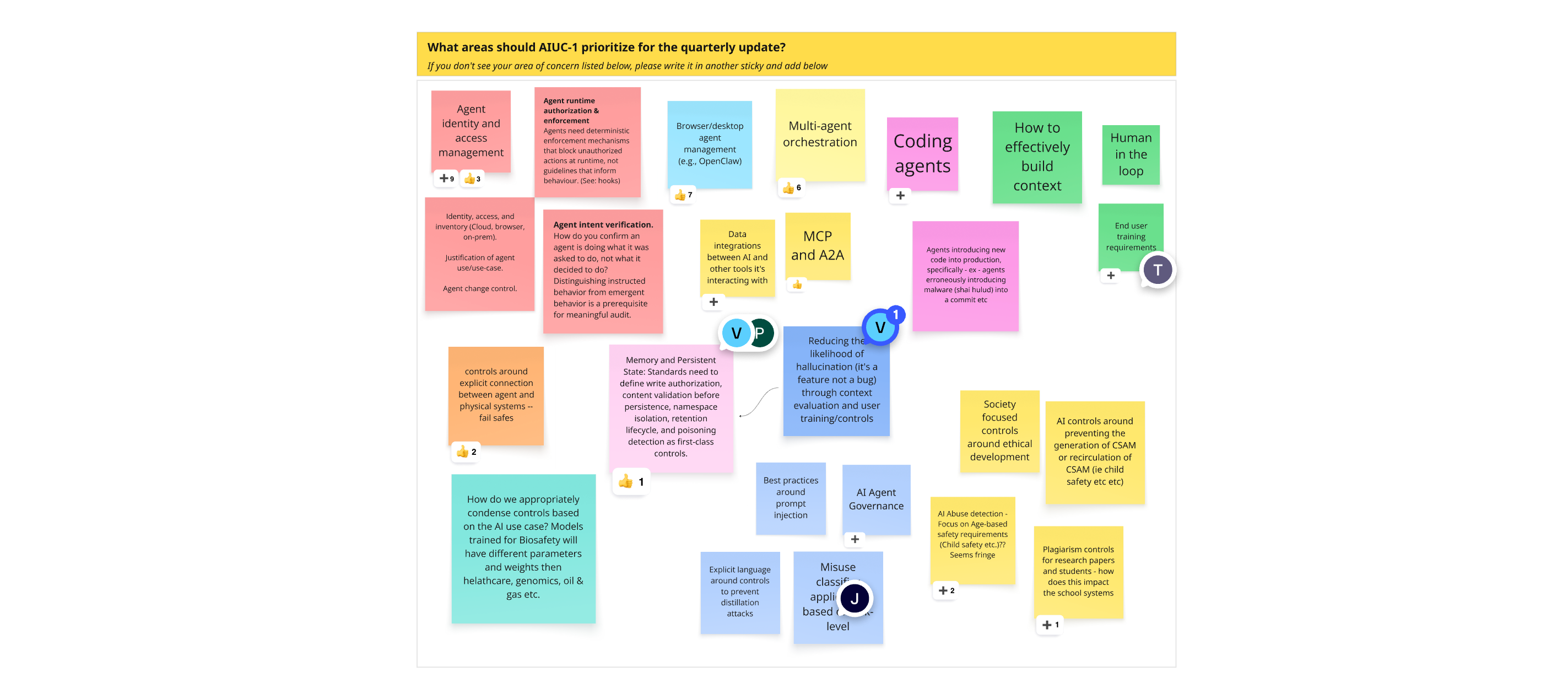
Miro Board output from initial prioritization session
Step 2: Technical working sessions
Once priority areas are defined, a series of technical working sessions begin. Through these sessions, risk areas are clarified, challenges are discussed, and updates/new controls are proposed. Sessions typically combine expert speakers and hands-on workshopping.
This quarter, technical sessions focused on securing multi-agent orchestration via MCP and A2A, and on agent identity, permissions and access management. The sessions shed light on real-world deployment experience from Consortium members and identified best practices mature enough to include in this quarterly update.
Step 3: Peer-review of proposed standard updates
Once proposed changes and new controls are finalized, the Consortium is engaged in a full peer-review process, which also activates AIUC-1 Technical Contributors including security and legal experts.
Through the peer-review, proposed changes are refined, application of controls (optional vs. mandatory) is debated based on adoption experiences, gaps and overlaps are flagged, and the entire control library is pressure tested.
This quarter, more than 200 comments were exchanged, all of which directly shaped the final update.
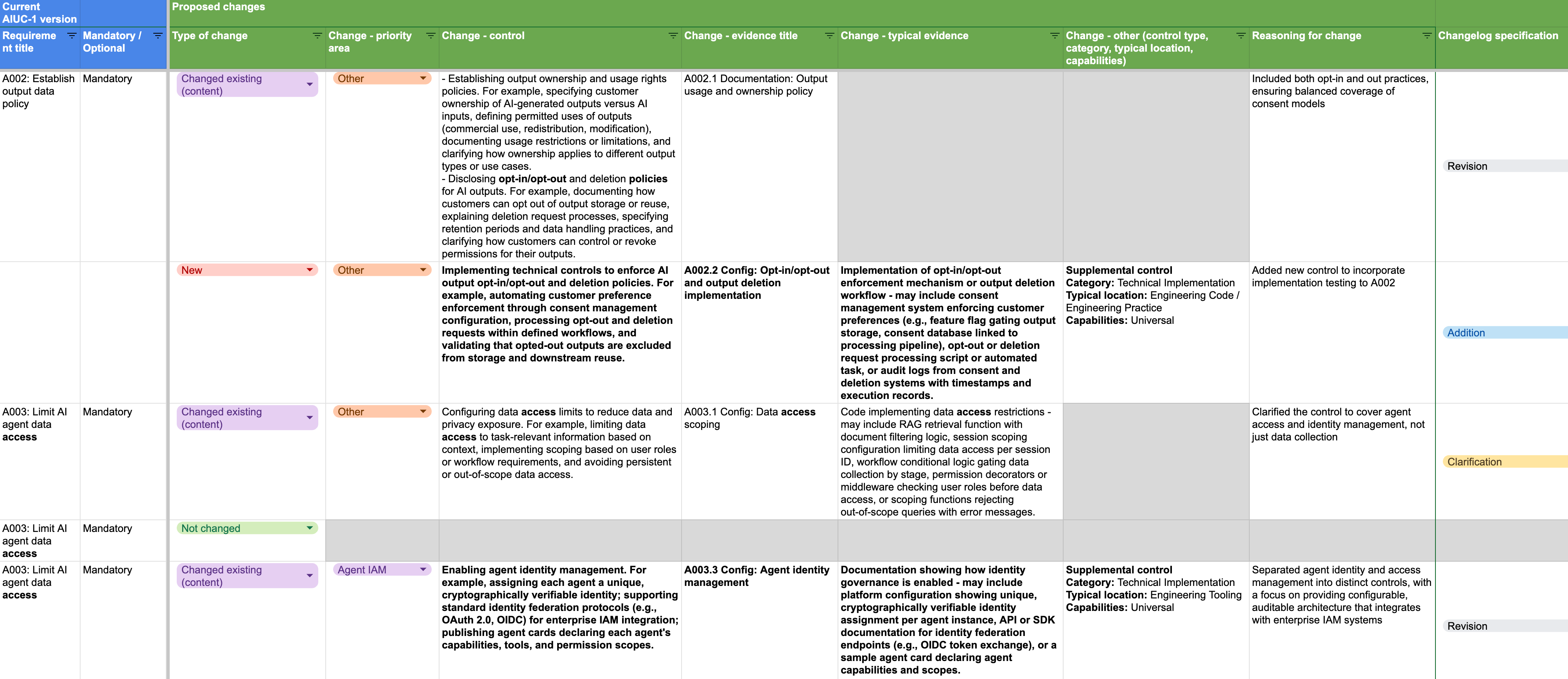
Excerpt of standard changes undergoing peer-review
Step 4: Launching the quarterly update with transparent change management
To enable full transparency, we document the changes made between each quarter’s standard requirements and controls, including the type of change, with detailed change notes and reasoning.
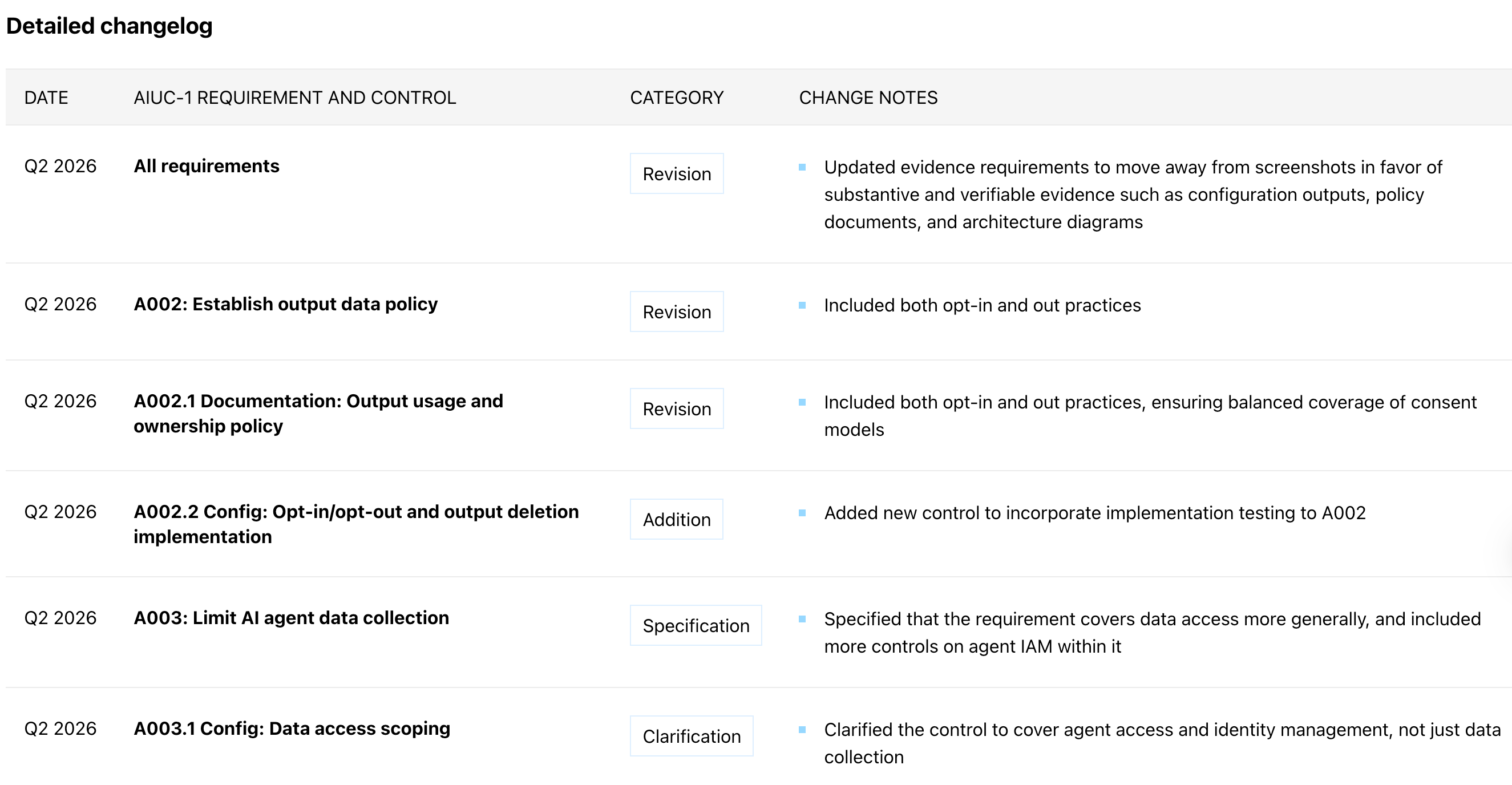
The full changelog of this quarterly update can be found here.
Step 5: Priorities for future updates
This quarter, 14 requirements and 23 controls were updated or added. However, the update process and recent step changes in AI capabilities have uncovered several additional areas demanding attention.
Examples include:
- Mythos Preview implications: A week before the release of this quarterly update, Anthropic released research on the capabilities of their latest model. Mythos has already found thousands of high-severity vulnerabilities, including some in every major operating system and web browser. This naturally demands changes to AIUC-1 in areas such as defensive AI cyber capabilities, adversarial robustness, and vulnerability management
- Third-party risk: This quarter, several standard updates were made to strengthen security of MCP servers and connections with third-party agents. Third-party risk remains a priority area for the upcoming quarterly update, particularly given the incident frequency, and many more ideas for how this could be managed were shared in the peer-review
Other areas where further work is ongoing include strengthening controls for coding agents, expanding controls for agent identity management, establishing controls for orchestrator agents, re-evaluating control applications based on risk, and 15+ additional areas of feedback received from Consortium members that will shape the July 15 version of AIUC-1.
Recognizing Consortium members
Going through this process each quarter demands immense engagement. We are grateful to AIUC-1 Consortium members and Technical Contributors for their time, insights, and detailed contributions that shape each quarterly update.
We welcome feedback, ideas, suggestions, and criticism - provide input on AIUC-1 here.
An executive summary of the standard updates this quarter can be found here.
Latest articles